Strengthening Defenses Against Identity Theft: A Look at Modern Prevention Strategies
Strengthening Defenses Against Identity Theft: A Look at Modern Prevention Strategies
Blog Article
In today's increasingly digital world, protecting your personal information is more critical than ever. Identity theft has become a rampant problem, with criminals finding increasingly sophisticated methods to steal sensitive data and financial resources. Fortunately, there are a number of proactive measures you can take to bolster your defenses against this growing threat. One of the most fundamental strategies is to adopt strong passwords and practice good password hygiene. Avoid using easily guessable passwords or the same password across multiple accounts. Instead, opt for long, complex passwords that contain a mix of uppercase and lowercase letters, numbers, and symbols.
Additionally, implement multi-factor authentication whenever possible. This adds an extra layer of security by requiring you to provide multiple forms of identification before granting access to your accounts. Be cautious about sharing personal information online or over the phone, and be wary of phishing scams that attempt to manipulate you into revealing sensitive data. Regularly monitor your bank statements and credit reports for any suspicious activity, and promptly report any potential fraud to the appropriate authorities. By implementing these modern prevention strategies, you can significantly decrease your risk of becoming a victim of identity theft and protect your financial well-being.
Exploring the Complex Landscape of copyright Laws and Regulations
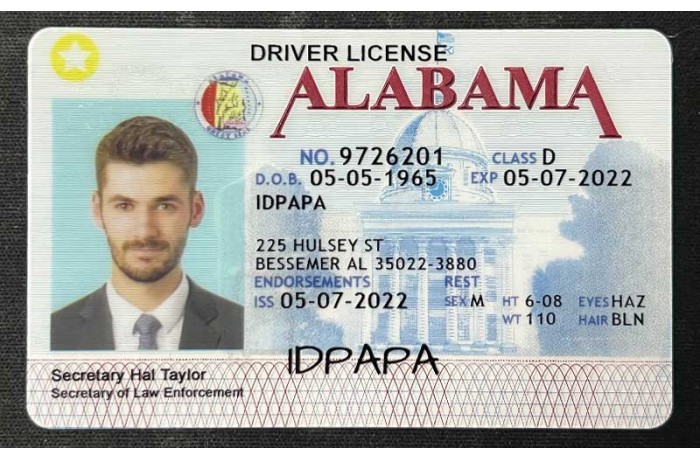
The world of fake identification is a constantly evolving one, with laws and regulations varying widely from jurisdiction to jurisdiction. Thinking about to get around these rules can lead to severe legal ramifications. It's essential for individuals to thoroughly understand the detailed laws governing copyright in their region to prevent potential trouble.
Educating yourself with the various penalties for manufacturing copyright can give valuable knowledge into the seriousness of the outcomes.
- Furthermore, staying informing yourself on any recent legal developments is highly advised to ensure you are acting within the bounds of the law.
Biometric Authentication: A New Era in Identity
As technology continues to progress, the need for robust and secure identity verification methods has never been more urgent. Traditional authentication methods, such as passwords and PINs, are increasingly susceptible to fraudulent activity. Biometric authentication presents a promising solution by leveraging unique biological characteristics to verify identities. From fingerprint and facial recognition to iris scanning and voice verification, biometrics offer a higher level of security and convenience compared to conventional methods.
- Biometric systems are inherently more complex to forge, as they rely on naturally occurring traits that are unique to each person.
- Moreover, biometrics can be seamlessly integrated into a variety of devices and platforms, boosting the user experience.
- As biometric technology continues to progress, we can expect even more advanced applications in fields such as finance, healthcare, and government.
The future of secure identity verification undoubtedly lies in the realm of biometrics. By embracing this transformative technology, we can create a more protected digital world for all.
Strengthening Security with Cutting-Edge Identity Verification Technology
In today's digitally driven world, safeguarding sensitive information has become paramount. Cyber threats are constantly advancing, making it imperative for organizations to implement robust security measures. Cutting-edge identity verification technology plays a crucial role in this endeavor by providing advanced mechanisms to authenticate user identities and prevent unauthorized access. By leveraging biometrics, artificial intelligence, and multi-factor authentication, businesses can create a secure environment that protects data.
- Moreover, these technologies can help reduce the risk of fraud and identity theft by implementing real-time monitoring and anomaly detection systems.
- Therefore, organizations can enhance their security posture, build trust with customers, and maintain compliance with industry regulations.
Combating Fraudulent Identities: Best Practices for Businesses and Individuals
Protecting yourselves from fraudulent identities is crucial in today's digital landscape. Companies must implement robust security measures to defend sensitive customer information. This includes multi-factor authentication, regularly updating software, and conducting thorough employee background checks. Individuals can also take steps to limit their risk by monitoring credit reports, using strong passwords, and remaining vigilant towards phishing scams. By working together, businesses Impact of fake IDs on society and individuals can strongly mitigate the threat of fraudulent identities.
Securing Your Digital Footprint: A Comprehensive Guide to Identity Theft Prevention
In today's interconnected world, safeguarding your personal information is paramount. Your online presence can reveal a wealth of private data that cybercriminals can exploit for nefarious purposes. Data breaches are increasingly common, emphasizing the urgent need to protect yourself.
- Adopt strong and unique passwords for each of your online accounts.
- Keep up-to-date your software, including operating systems and applications.
- Exercise caution when sharing personal information online.
By following these fundamental steps, you can lessen your risk of becoming a victim of identity theft and maintain your digital well-being.
 Report this page
Report this page